Patch a thing: Securing Internet of Things (IoT) devices
July 16th 2019 update: List of IoT (Internet of Things) security solutions
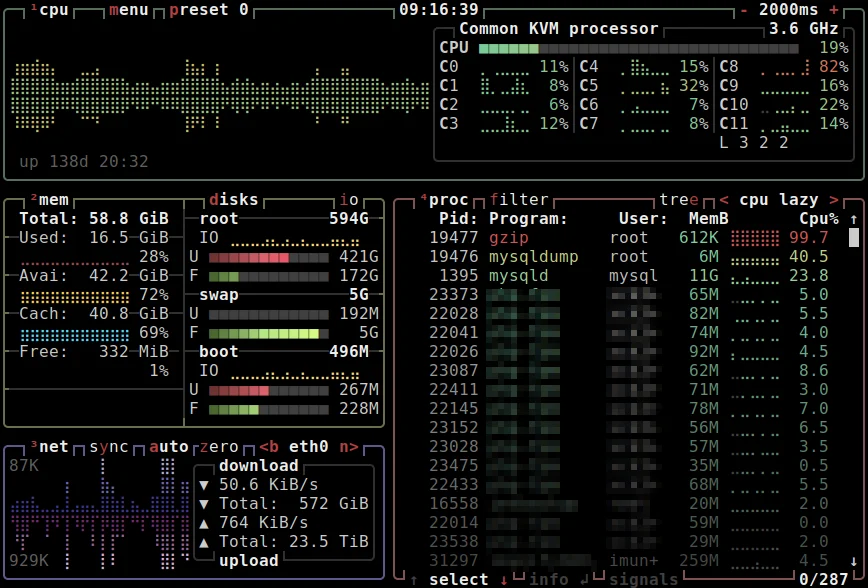
Today, I spent some time researching IoT security. At the end of this post, I’ve listed companies – all of which are new to me – which offer IoT security solutions. Feel free to share your solutions, feedback and tips for securing IoT devices. For my home office, everything sits behind an OpenWRT Wi-Fi router which allows for custom firewall config.
In the aftermath of yesterday’s DDoS cyber attack on DYN’s DNS servers, a few key questions arise. The most important being: How do we protect IoT devices from future compromise? DDoS attacks are not new, however DDoS attacks using IoT devices are. There are millions of these devices connected to the internet. That number is growing rapidly with the explosion of the IoT industry (See my ‘Device Health’ quote). The DDoS attacks on October 21st 2016 were already predicted almost a year in advance, yet the question was then, and is now… How do you patch a ‘thing’?
That’s part of the problem, many smart TVs and other IoT devices are limited to just firmware updates and cannot be patched for specific security flaws. In addition, limited or non-existent UIs (user interfaces) is another contributing factor to IoT’s lack of security. As Deepinder Singh, founder of 75F humorously puts it: “When was the last time somebody logged into their light bulbs to do a tcpdump to check if there were rogue packets?”. Unlike web servers, computers, smartphones and other security minded internet connected devices, many IoT devices lack built in security features such as a basic firewall or strong passwords.
Securing Internet of Things (IoT) devices
IoT manufacturers for the most part use cheap components and boards which lack the power or capability to run fundamental security features, such as anti-malware, anti-virus, firewalls and encryption. These devices are thus left not only vulnerable, but worst, making them virtually impossible to secure. So sadly there’s no quick fix. Only mitigation of future attacks and other preventative measures by companies such as DYN and others will suffice. As for the IoT devices, the direction towards solving this security threat will require a combined effort from consumers, manufacturers and techs.
For consumers with IoT connected devices, your IoT devices should always exist behind a Firewall. Also, the default firewall settings and passwords of many WiFi routers and devices are not adequate to block such traffic. As such, you should hire an expert to audit your home and office network security. By 2020, it is estimated that the number of connected devices is expected to grow exponentially to 50 billion!
To address the security issues at the manufacturing level of IoT devices, there needs to be strict security standards and regulations put in place. This however, is a mammoth task. Thankfully, many IoT devices will age, become obsolete or even be recalled. With newer versions being released, this gives manufactures the opportunity to beef up built-in security. SysAdmins should investigate and compare solutions which focus on protecting all on-premise devices. Having for example gateways and/or firewalls in place which add a layer of protection in front of IoT devices. This is especially important because, as mentioned, IoT devices often have limited compute resources and are for the most part unable manage their own security on-board. Think of IoT devices as toddlers as it were, when it comes to security and they are in need of parenting and stranger-danger protection.
Here’s a continuously updated list of current IoT security solutions [will expand this section as I check into these solutions in more detail]: Subex IoT Security, CUJO – Smart Firewall, Dojo security of things, Bitdefender BOX – IoT Security Solution, F-Secure for Home and Business, ZingBox | IoT Security for the Enterprise, Luma – Safe, Family-Friendly Internet.
(Post additional solutions in the comments section below, or contact me and I’ll add missing solutions above.)