Generating Secure Passwords for your Linux Server
Update: March 4th 2024: While the guidance below – originally provided in 2013 – emphasizes the creation and management of secure passwords, more than a decade later, it’s important to recognize and advocate for the use of passwordless authentication methods wherever feasible.
Authentication keys for SSH, biometric authentication, and single sign-on (SSO) are exemplary alternatives that bolster security and enhance user convenience.
Passwordless authentication methods offer several compelling advantages:
- Enhanced Security: By eliminating passwords, you reduce the risk associated with password theft, phishing attacks, and brute-force attempts. Authentication keys and biometrics are considerably harder for malicious actors to compromise.
- Improved User Experience: Users no longer need to remember complex passwords or undergo frequent password resets, streamlining access and reducing support requests related to password issues.
- Simplified Management: For administrators, passwordless systems can simplify user management and security protocols, as there’s no need to enforce password policies or manage password databases.
Embracing Passwordless Authentication
In the broader landscape of cybersecurity, moving towards passwordless authentication represents a forward-thinking approach that aligns with evolving security standards and user expectations.
While not all systems and services support passwordless options today, prioritizing these methods, where available, can significantly enhance the overall security posture of your server environments and user ecosystems.
By fostering an environment that values advanced security measures over traditional password-dependent methods, we can pave the way for a more secure and user-friendly digital world.
System administrators are often tasked with the crucial role of establishing and reinforcing server safeguards. This encompasses various tasks, from deploying new servers to enhancing the security of existing ones, with a particular focus on creating robust passwords for various services such as SFTP and administrative panels.
Despite the broad spectrum of security practices available, the importance of secure passwords is frequently overlooked, yet it remains a cornerstone of a fortified server environment.
A common misconception is that all server aspects, including SSH and MySQL root passwords, require remote password access for security. However, if your commitment to security is unwavering, these components should be configured to eschew remote password login entirely.
For SSH access, the utilization of authentication keys coupled with the deactivation of password authentication (by setting PasswordAuthentication no in your SSHD configuration file) is advised.
Similarly, for MySQL, implementing setting skip-networking andbind-address = 127.0.0.1, alongside leveraging iptables to block or restrict port 3306 to designated IP addresses, enhances security. Direct socket connections are recommended for local MySQL communication if the database resides on the same server.
Also, read the article Passwordless Authentication Services.
Generating secure passwords
For selecting secure passwords, here’s what is recommended:
- Passwords should be a minimum of 16 characters to ensure complexity.
- A mix of uppercase and lowercase letters, numbers, and special characters should be included to enhance security.
Using pwgen to generate a secure password
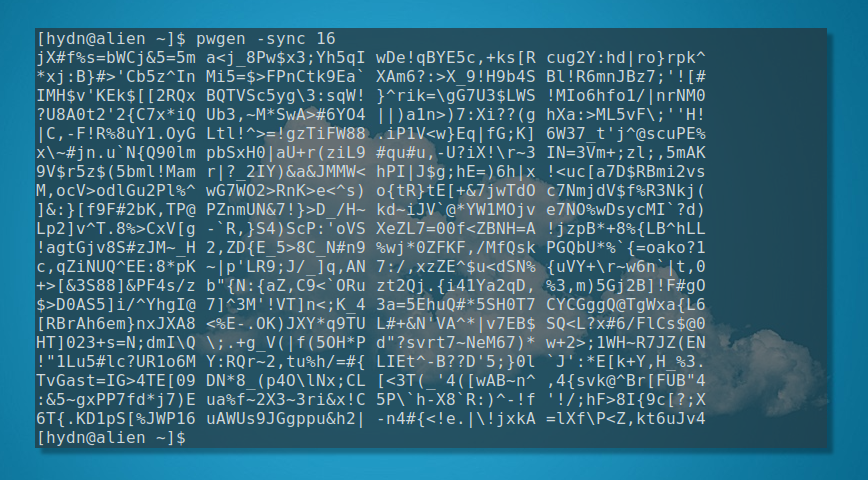
Here’s my go-to command-line method for secure password generation. The command I use is:
pwgen -y 32
Even more secure and easy to remember using the word ‘sync’:
pwgen -sync 16
The pwgen command is an efficient tool for generating secure passwords directly from the command line. For a robust password, the command pwgen -y 32 is highly recommended, generating a 32-character password with at least one special character.
For passwords that are secure but shorter use pwgen -sync 16, can be beneficial. It’s not recommended to create passwords shorter than 16 characters.
pwgen is widely available across Linux distributions and can typically be installed via the system’s package manager, using commands like apt install pwgen or dnf install pwgen. Read more about pwgen.
Once installed, here’s an explanation of the command I’m using above. You can fine-tune it to meet your needs:
-s, --securegenerates random, hard-to-memorize passwords.-y, --symbolsensures the inclusion of special characters.-n, --numeralsadds numeric characters.-c, --capitalizeincorporates at least one uppercase letter.- Specifying
16sets the desired length of the generated passwords.
Need fewer generated passwords? Use pwgen -sync 16 1 where 1 = the number of password results.
Using ‘pass’ to generate a secure password
With pass, each password lives inside a gpg encrypted file whose filename is the title of the website or resource that requires the password. These encrypted files may be organized into meaningful folder hierarchies, copied from computer to computer, and, in general, manipulated using standard command-line file management utilities. Thus, pass is also a command-line password manager.
This is an updated article from 2013. Here’s the previous method from the original article…
Use the urandom command to generate secure passwords
Recommended urandom
< /dev/urandom tr -dc '[:graph:]' | head -c16;echo;
Right-hand only urandom
< /dev/urandom tr -dc '67890^*_+-=;:,.?yuiopYUIOPhjklHJKLbnmBNM' | head -c16;echo;
Left-hand only urandom
< /dev/urandom tr -dc '12345!@#$%qwertQWERTasdfgASDFGzxcvbZXCVB' | head -c16;echo;
Making this into a simple easy to remember command
Edit your bashrc
vi ~/.bashrc
Add this line:
spw(){ insert one of the above options here }
Example:
spw(){ < /dev/urandom tr -dc '[:graph:]' | head -c16;echo; }
Save and restart the server, or even better, reload bash using:
source ~/.bash_profile
Now in the future, type the following to generate a secure password:
spw
![]()
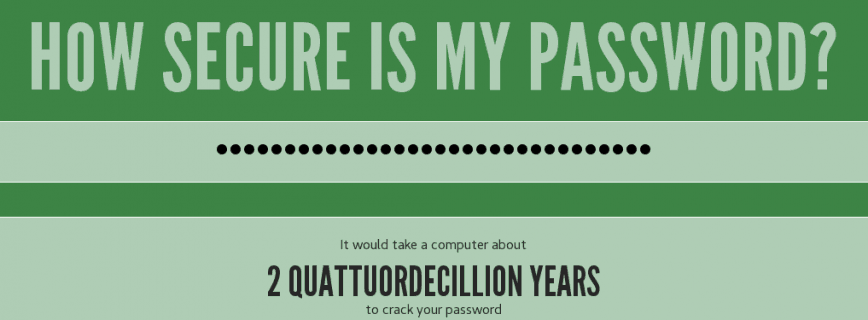
It would take trillions of years to crack your password using these methods. This is why a strong password is essential.
Other Linux commands use OpenSSL, dd, and date to generate passwords, but urandom pwgen is my preferred method. Feel free to add your methods below.
Also, remember, you should have security to avoid brute force password cracking. For example, after five failed attempts, the IP should be blocked and reported (for example, abuseipdb.com).
Conclusion
While the focus on tools like pwgen and pass is useful, it’s crucial to remember that password strength is just one facet of server security. Implementing measures to thwart brute-force attacks, such as IP blocking after consecutive failed login attempts, complements the use of strong passwords.
As threats evolve with increasing sophistication, the commitment to adopting and integrating advanced security practices, especially passwordless options, becomes crucial.
Published: November 23rd, 2013 | Last updated: March 4th, 2024
What perfect timing to be seeing this on the forum. I am getting ready to start my first Linux based server so this is handy to know. Security is super important, as we all know and setting it up right for a server is crucial. Are there any other sources you can link me to for setting up a Linux server for the first time?
I still haven’t got behind using authentication keys for SSH yet. If I lose the key, I’m permanently locked out aren’t I? It seems a complex password is a better choice. I also use MFA to protect SSH which seems to be as good as security can get. Definitely open to being shown that I am wrong, definitely no expert here.